Banner Grabbing
Telnet Banner Grab
telnet 10.10.182.147 80
GET / HTTP/1.0
host: telnetGET / HTTP/1.1
host: telnet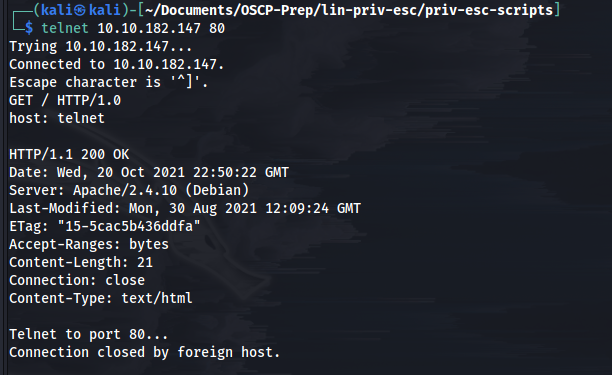
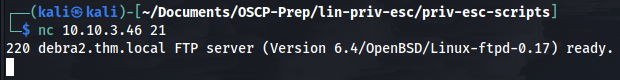
NetCat Banner Grab
NetCat FTP Banner Grab
Openssl banner grab
HTTP Header Grabbing (curl)
Last updated